This guide explores the obscure yet complex AAVSVAVSVS:SSVBSVSCNSVSVBzo1234 sequence and delves into its implications in various fields. While the term seems randomly generated, its potential significance or application could be vast, especially in areas such as digital coding, cybersecurity, or cryptography. This article attempts to demystify this keyword, examining potential contexts and uses from an expert's viewpoint.

The cryptic string AAVSVAVSVS:SSVBSVSCNSVSVBzo1234 presents an enigmatic challenge not just for linguists but also for experts in fields such as coding, cryptography, and cybersecurity. At first glance, this alphanumeric sequence might appear to be random; however, like many coded languages, its complexity suggests hidden meanings or applications worth exploring. With the rapid evolution of technology and the increasing sophistication of cyber threats, understanding and decoding such sequences can become essential for maintaining digital security.
In the realm of digital coding and cryptography, sequences like AAVSVAVSVS:SSVBSVSCNSVSVBzo1234 could serve several functions. Experts speculate that such an arrangement could be part of a unique encryption key, a coded message, or a digital signature for secure data transmission. Within these fields, understanding the structure and potential functionalities of such sequences is fundamental to enhancing security protocols and systems. As technology evolves, so too does the creativity involved in coding and encryption methods. The examination of such sequences could allow researchers to identify emerging trends in cryptographic techniques and the interplay between linguistics and information security.
To better understand the significance of mysterious sequences, a retrospective view into the history of cryptography helps reveal how far the field has come. The ancient practices of cryptography, from the Caesar Cipher to the Enigma machine used during World War II, showcase how encoding methods have evolved over millennia. These rudimentary forms of encryption relied heavily on letter substitution and simple mechanical devices. However, today's cryptographic landscape employs complex algorithms that can adapt and respond to an extremely dynamic digital environment. Sequences like AAVSVAVSVS:SSVBSVSCNSVSVBzo1234 may be indicative of a new chapter where cryptography converges with fields like quantum computing, further complicating the ciphering techniques and security measures.
To decipher the significance of AAVSVAVSVS:SSVBSVSCNSVSVBzo1234, cryptanalysis methods could be employed. Techniques involving frequency analysis, reverse engineering, and pattern recognition are commonly used by professionals to unravel such cryptographic mysteries. Each method provides insight into the sequence's composition, potentially unveiling unique patterns or intended messages concealed within the complexity. For instance, frequency analysis examines how often certain characters or sequences appear in the encoded text, which can be instrumental in cracking ciphers. Conversely, reverse engineering takes a more holistic approach, attempting to deconstruct the sequence based on known principles of cryptography.
| Cryptanalysis Method | Description |
|---|---|
| Frequency Analysis | Studying the frequency and pattern of characters in order to find hidden meanings. This method often highlights the most common letters in a given language, which can streamline efforts to decode a cipher. |
| Reverse Engineering | Deconstructing sequences to understand their construction and purpose, revealing potential vulnerabilities in the coding process or pointing towards effective decryption strategies. |
| Pattern Recognition | Identifying recurring sequences or symbols to unravel encoded messages; this technique relies on recognizing visual or structural motifs within code. |
| Brute Force Attacks | A trial-and-error method where attackers systematically try every possible key combination until the correct one is discovered. |
| Chosen-Plaintext Attack (CPA) | In this method, cryptanalysts can obtain the ciphertext corresponding to particular plaintexts, enabling them to deduce the encryption key by analyzing how specific plaintexts are transformed into ciphertexts. |
| Statistical Analysis | Involves the application of statistical methods to determine patterns in encoded information, often revealing biases or common errors that can be exploited for decryption. |
| Known-Plaintext Attack (KPA) | Using both known plaintext and its corresponding ciphertext to discover the key used for encryption, this method often enables faster breakthroughs in deciphering complex sequences. |
A robust sequence like AAVSVAVSVS:SSVBSVSCNSVSVBzo1234 might find its place in cybersecurity tools designed to protect sensitive information against unauthorized access. Cybersecurity experts constantly develop sophisticated algorithms to keep pace with threats, and applying complex sequences could bolster encryption methods, making it painstakingly difficult for cybercriminals to decipher protected data. For instance, the integration of randomized sequences within a multi-layered encryption framework significantly enhances security measures against potential attacks.
Data breach incidents have highlighted the necessity for advanced encryption techniques. Leveraging sequences such as AAVSVAVSVS:SSVBSVSCNSVSVBzo1234 could potentially enhance the strength of algorithms used to protect sensitive data. In turn, by increasing the complexity of these sequences, institutions can fortify their digital fortifications against evolving threats. Beyond safeguarding individual data packets, this complexity might also contribute to building trust in digital communications, ensuring that both enterprises and users feel secure in their online interactions.
Furthermore, the incorporation of dynamic sequences in modern security practices can lead to adaptive encryption systems capable of self-evolving based on emerging threats. As cyber adversaries grow increasingly resourceful, creating layers of multiple sequences that are continually updated in response to attacks could form a critical line of defense.
Beyond cybersecurity, cryptographic applications could see pioneering uses for sequences like AAVSVAVSVS:SSVBSVSCNSVSVBzo1234. The encryption of sensitive communications, securing online transactions, and authenticating user identities in digital ecosystems are all potential fields harnessing the power of such cryptic sequences. In today’s world where sensitive information is shared online daily, the reliance on strong cryptographic systems is more pressing than ever.
Innovations in blockchain technology have also opened avenues for applying complex sequences in smart contracts, decentralized finance (DeFi), and secure identity verification mechanisms. These advancements in cryptography symbolize a leap forward in ensuring data privacy in an interconnected world. As organizations and industries adopt these technologies, it becomes increasingly essential to explore the potential uses of complex sequences in securing their operations.
As artificial intelligence (AI) and machine learning capabilities develop, we anticipate revolutionary changes in cryptographic practices. Predictive algorithms could identify vulnerabilities and potential attack pathways, allowing for preemptive adjustments to encoding methodologies. Moreover, quantum computing presents both a challenge and an opportunity for cryptography, as traditional encryption methods risk becoming obsolete against quantum attacks. This emerging field emphasizes the importance of developing new algorithms capable of resisting the superior computational power of quantum technologies.
The future of sequence analysis may include leveraging AI to enhance cryptanalysis techniques, automating processes that presently require significant human intervention. The combination of human curiosity, creativity, and machine intelligence could yield robust encryption solutions that meet the developing challenges of cybersecurity.
For everyday users and businesses alike, the cryptographic foundation underdeveloped sequences affects data security and personal privacy in significant ways. Encryption remains key in shielding individual communications, financial transactions, and sensitive corporate information. The implications extend to various sectors, including finance, healthcare, and personal communications, where a breach could have severe consequences. Institutions emphasizing strong encryption methods based on complex sequences display their commitment to safeguarding users' information.
Furthermore, as users become more informed about digital security, their expectations for safe online experiences rise. Businesses must respond by adopting more sophisticated encryption protocols supported by continuous advancements in sequence analysis and cryptographic practices. The integration of comprehensive training initiatives can empower employees to understand potential threats and best practices for keeping data secure.
Although this sequence seems random, it may have cryptographic or coding significance, potentially used in encryption or data protection. Its composition hints at the evolution of complex encoding techniques that play a crucial role in safeguarding digital information.
These sequences might be utilized in fields like cybersecurity, cryptography, secure communications, and digital transactions, all of which rely on advanced encryption techniques to protect sensitive information.
They create complex keys vital for encrypting and protecting sensitive data from unauthorized access and cyber threats. The application of intricate sequences aids in building trustworthy systems for online activities.
Cryptography adapts continuously, leveraging advancements in AI, machine learning, and quantum computing. These technologies prompt the redesign of encryption algorithms to counteract potential vulnerabilities that emerge with new computational capabilities.
Individuals should adopt practices such as using strong, unique passwords, enabling two-factor authentication, and regularly updating security software. Awareness of potential phishing schemes and the importance of encrypted communication should also be prioritized.
The enigmatic sequence AAVSVAVSVS:SSVBSVSCNSVSVBzo1234 exemplifies the intrigue and potential found in seemingly random assemblies of characters. As technology advances, understanding—and harnessing—the potential of such sequences becomes paramount, especially for cybersecurity and cryptography experts striving to safeguard the digital realm. Whether or not this particular sequence has been actively applied, its study furthers our understanding of encryption potential and innovative data protection methods. By examining the layers of complexity contained in sequences like AAVSVAVSVS:SSVBSVSCNSVSVBzo1234, we foster a deeper appreciation for the critical intersection of technology, security, and communication in our increasingly interconnected world.
Ultimately, the quest to decode and apply mysterious sequences stretches beyond academia and into the fabric of modern life, entwining with our daily digital experiences and the critical infrastructures that support them. As we venture further into the digital age, the call for robust security measures and sophisticated cryptographic techniques remains a foremost concern, making the exploration of sequences not just an academic endeavor but a vital necessity for the safety and integrity of the information age.
Striking the Perfect Balance: Navigating Premiums and Out-of-Pocket Expenses in Senior Insurance Plans

Explore the Tranquil Bliss of Idyllic Rural Retreats

How to Make Lasting Memories at Disneyland Attractions

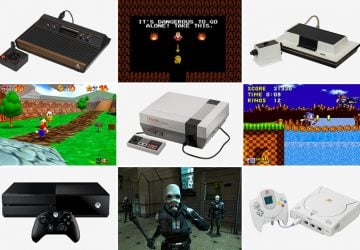
Ultimate Countdown: The 20 Very Legendary Gaming Consoles Ever!
Understanding Halpin and its Influence

Affordable Full Mouth Dental Implants Near You

Unlock the Top Kept Secrets to Finding Your Ideal Dentist for Flawless Dental Implant Results!

Discovering Springdale Estates

Illinois Dentatrust: Comprehensive Overview
